Featured Products
A cybersecurity incident can escalate quickly if teams do not have a clear process for identifying, containing, and recovering from threats. This Incident Response Plan provides a structured framework for managing security incidents while minimizing operational disruption and protecting sensitive data.
What’s Included
Incident Response Governance Framework
Incident Severity Classification Matrix
Incident Response Team Structure
Incident Escalation Process
NIST Aligned Incident Lifecycle (Identification → Containment → Eradication → Recovery → Review)
and more…
Who This Is For
Organizations that:
Do not currently have a formal incident response plan
Need to demonstrate security maturity to clients or auditors
Want to ensure leadership and IT teams understand their roles during an incident
Format
Editable document format designed to be customized for your organization.
A starter kit to prepare your organization for and respond to cyber incidents.
The Incident Response Starter Toolkit provides a framework for managing cybersecurity incidents. It combines a structured Incident Response Plan with practical playbooks covering the most common types of cyber incidents.
This toolkit gives organizations the procedures needed to respond quickly, coordinate leadership decisions, and restore operations when security incidents occur.
What’s Included
Incident Response Plan
Playbooks for:
Phishing & Credential Compromise
Ransomware
Cloud Data Exposure
Malware Infection
Lost or Stolen Device
Business Email Compromise
Additional resources:
Incident Severity Classification Matrix
Incident Response Team Structure
Evidence Preservation Guidelines
Incident Documentation Guidance
Who This Is For
Organizations that:
Do not currently have a formal incident response capability
Want a structured starting point for cybersecurity readiness
Need documented response procedures for clients, regulators, or auditors
Incident Response Playbook Bundle
Step-by-step response procedures for the most common cybersecurity incidents.
When a cyber incident occurs, teams often know something is wrong but are unsure what to do next. The Incident Response Playbook Bundle provides clear, structured guidance for responding to the most common cybersecurity incidents faced by modern organizations.
Each playbook walks through the response process using a practical framework that guides teams through investigation, containment, eradication, recovery, and post-incident review.
These playbooks are designed to support IT teams, leadership, and security personnel when responding to real-world incidents.
What’s Included
This bundle includes response playbooks for six of the most common security incidents.
Phishing & Credential Compromise
Respond to account takeover attempts and phishing attacks targeting employees or administrators.
Ransomware
Structured guidance for containing ransomware infections, protecting backups, and restoring business operations.
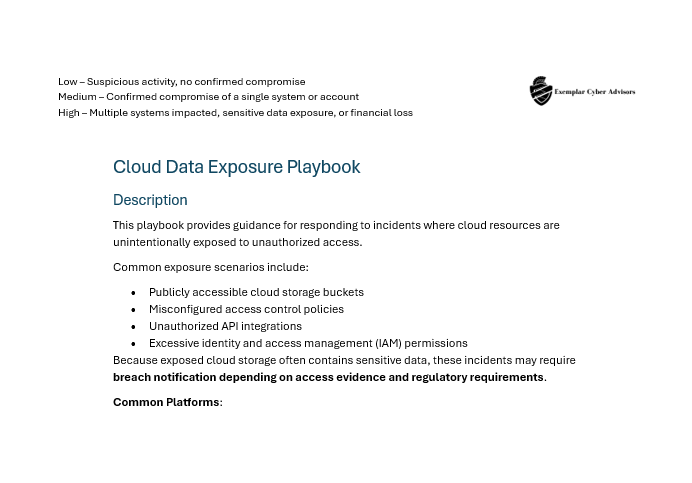
Cloud Data Exposure
Respond to misconfigured storage buckets, exposed databases, and unauthorized cloud access.
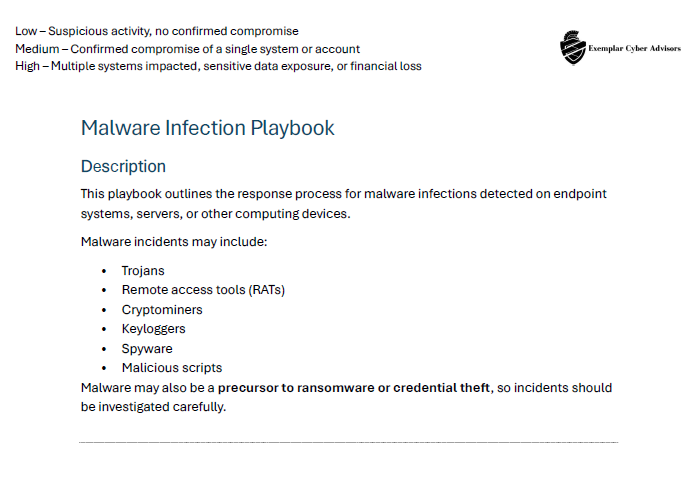
Malware Infection
Identify infected systems, isolate compromised devices, and remove attacker persistence.
Lost or Stolen Device
Assess risk and secure corporate accounts when company devices are lost or stolen.
Business Email Compromise (BEC)
Respond to fraudulent payment requests, vendor impersonation attacks, and financial fraud attempts.
Who This Is For
The Incident Response Playbook Bundle is designed for:
Small and mid-size organizations
IT teams responsible for security response
Companies building their first incident response capability
Organizations that need documented response procedures